COHORT BASED COURSES
Certificate In Cybersecurity
This course introduces students to the field of Cyber Security.
It provides an extensive overview of the various branches of this field, Cyber Security concepts, and issues that are critical to solving problems in the computing security domain.
Web Applications Security
This course offers extensive knowledge for every web developer and web application engineer.
A participant will discover important principles of modern web security, and learn about current security best practices.
Certificate In Information Security Practice
This course is specifically designed for cybersecurity professionals in managerial positions who aim to deepen their expertise in security practices, laws, and policy development. Participants will gain advanced knowledge to effectively manage cybersecurity risks, develop robust policies, and ensure compliance with relevant laws and regulations.
Certified Ethical Hacking
The Certified Ethical Hacker (CEH) program is the core of the most desired information security training system any information security professional will ever want to be in. The CEH, is the first part of a 3 part EC-Council Information Security Track which helps you master hacking technologies. You will become a hacker, but an ethical one!
CompTIA Security+
MCA partners with CompTIA to provide this course. CompTIA Security+ is a global certification that validates the baseline skills necessary to perform core security functions and pursue an IT security career. It establishes the core knowledge required of any cybersecurity role and provides a springboard to intermediate-level cybersecurity jobs.
CompTIA CySA+
MCA partners with CompTIA to provide this course. MCA partners with CompTIA to provide this course. CompTIA Cybersecurity Analyst (CySA+) is an IT workforce certification that applies behavioral analytics to networks and devices to prevent, detect and combat cybersecurity threats through continuous security monitoring.
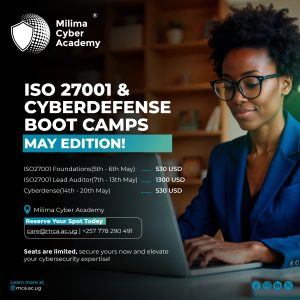
ISO 27001 & Cyberdefense Bootcamp
ISO/IEC 27001 provides requirements for organizations and individuals seeking to
establish, implement, maintain, and continually improve an information security
management system. The Cyberdefense training program is a unique cybersecurity training designed to
introduce participants to critical concepts of attacks and defense of the IT
infrastructure.
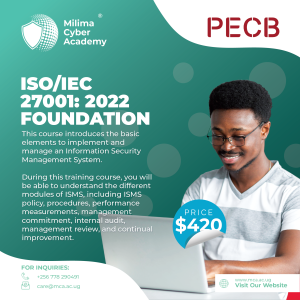
ISO/IEC 27001 Foundation
ISO/IEC 27001:2022 Foundation training allows you to learn the basic elements to implement and manage an Information Security Management System. During this training course, you will be able to understand the different modules of ISMS, including ISMS policy, procedures, performance measurements, management commitment, internal audit, management review, and continual improvement.
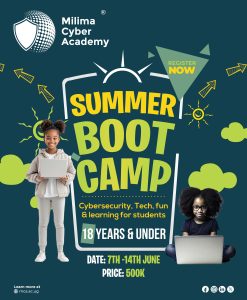
Summer Bootcamp
SUMMER BOOTCAMP | JUNE 7–14, 2025
Tech, fun & learning for students 18 & under!
Explore cybersecurity, Ethical Hacking, and more in a hands-on, playful environment.
📣 Register now and let the summer adventure begin!
CORPORATE TRAININGS
Cyber Defense Training
In this unique training, typical IT attacks are simulated in realistic virtual corporate networks.
The aim is to enable each participant to understand and defend against a wide variety of modern IT attacks.
Cyber Awareness Training
Our awareness training is designed to expose both the non-technical and technical users to latest Cyber threats, techniques hackers use to penetrate systems and how unsuspecting users are often used to complete the job easily. Through this training therefore users are then trained on how to detect threats, respond to threats and stay clear of common attack vectors used by attackers.
Cybersecurity for Executives
MCA supports organisational cyber-maturity through the delivery of information security audit services, an exercise aimed at discovering system weaknesses that could otherwise be exploited by hackers and bad actors. Through this exercise, an organisation is able to gain better insights into their security posture and make necessary improvements to avoid attacks, improve on compliance and present themselves to clients as a cyber-mature entity.
VIRTUAL REALITY POWERED CYBERSECURITY TRAINING

OUR PARTNERS







WHAT OUR ALUMNI SAY..


OUR STUDENTS COME FROM...













NEWS AND PUBLICATIONS
🛡️ Milima Cyber Academy Presents: The Ultimate Summer Bootcamp! 🌞💻
Calling all young tech enthusiasts! Join us this June for an unforgettable adventure into the world of Cybersecurity, Technology, and Fun at …
Enroll Now for the January 2025 Cybersecurity Courses! Are you ready to take the next step in your cybersecurity career? We are …
TOPIC: BUILDING A CYBERSECURITY CUTURE IN EMERGING FINANCIAL INSTITUTIONS WEBINAR Date: 25th October, 2024 …
ABOUT MCA
We are Uganda’s top-tier cyber-security and digital forensics academy supporting young professionals to gain practical and hands-on skills.
PAGES
- Home
- About Us
- Cyber Defense Training
- Cyber Awareness Training
- Publications
- FAQs